Create Security Group for DB
Create Security group for DB instance
-
We create a Security Group for the Database instance. To ensure security, do not configure the application’s Security group together.
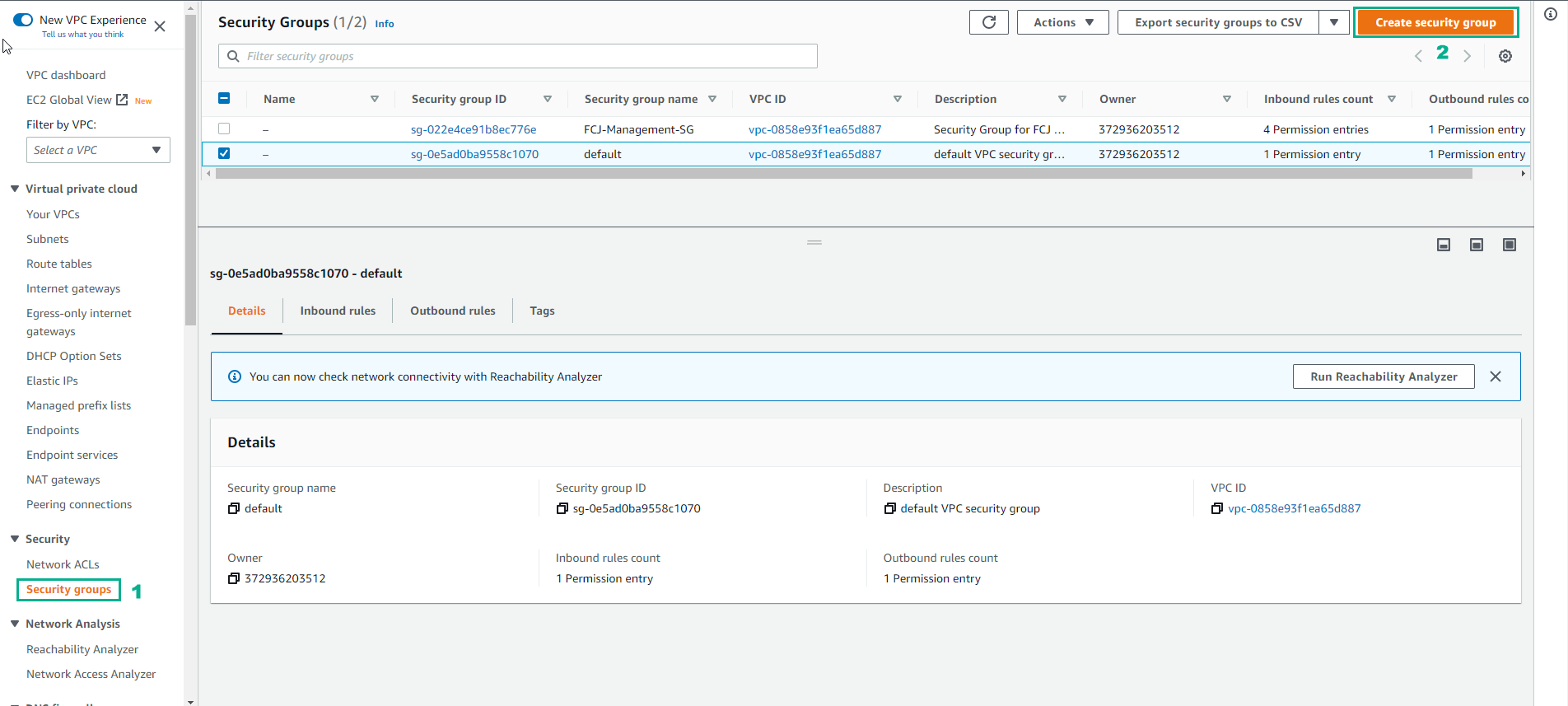
- Select Security Group
- Select Create a security group
-
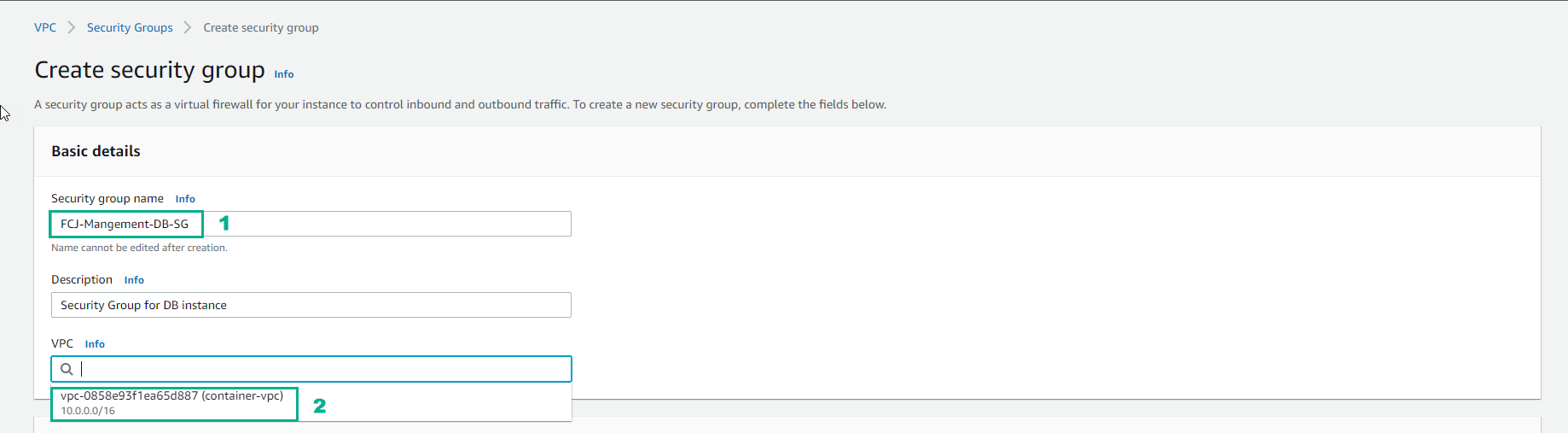
Practice security group configuration
- Security Group name, enter FCJ-Management-DB-SG
- Description, enter Security Group for DB instance
- Select the newly created vpc
-
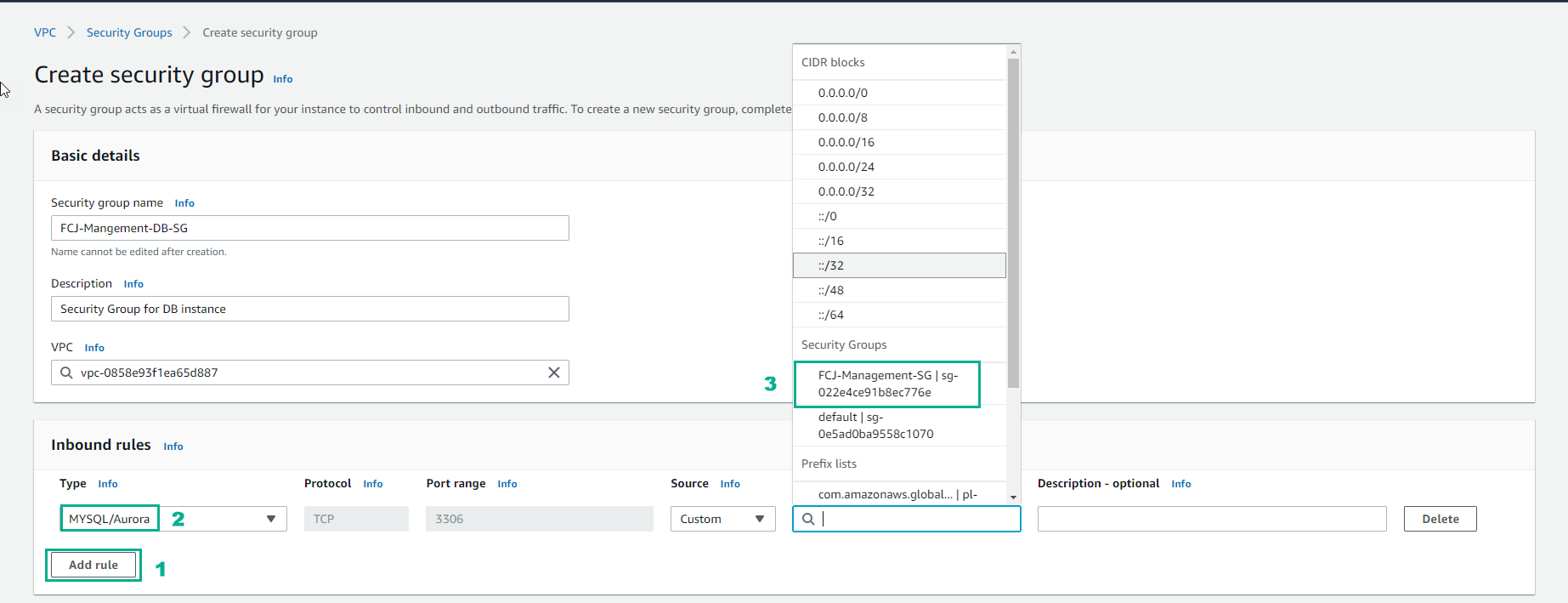
Configure Inbound rules
- Select Add rule
- Select MYSQL/Aurora port 3306
- Then select Source as FCJ-Management-SG
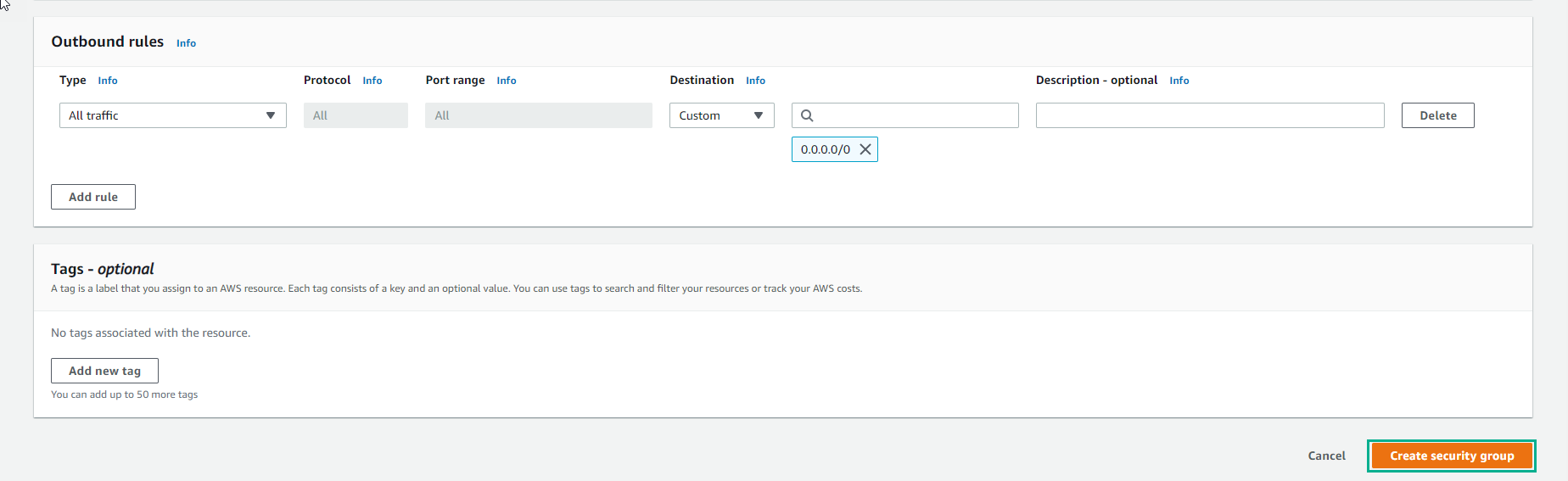
- Select Create a security group